Electronics | Free Full-Text | Evaluating the Effectiveness of Handling Abusive Domain Names by Internet Entities
Abuse Management for Domain Names - Cybersecurity & Data Protection – Public Security & Individual Freedom: doteditorial - Security & Trust in Digital Services - Issues - dotmagazine

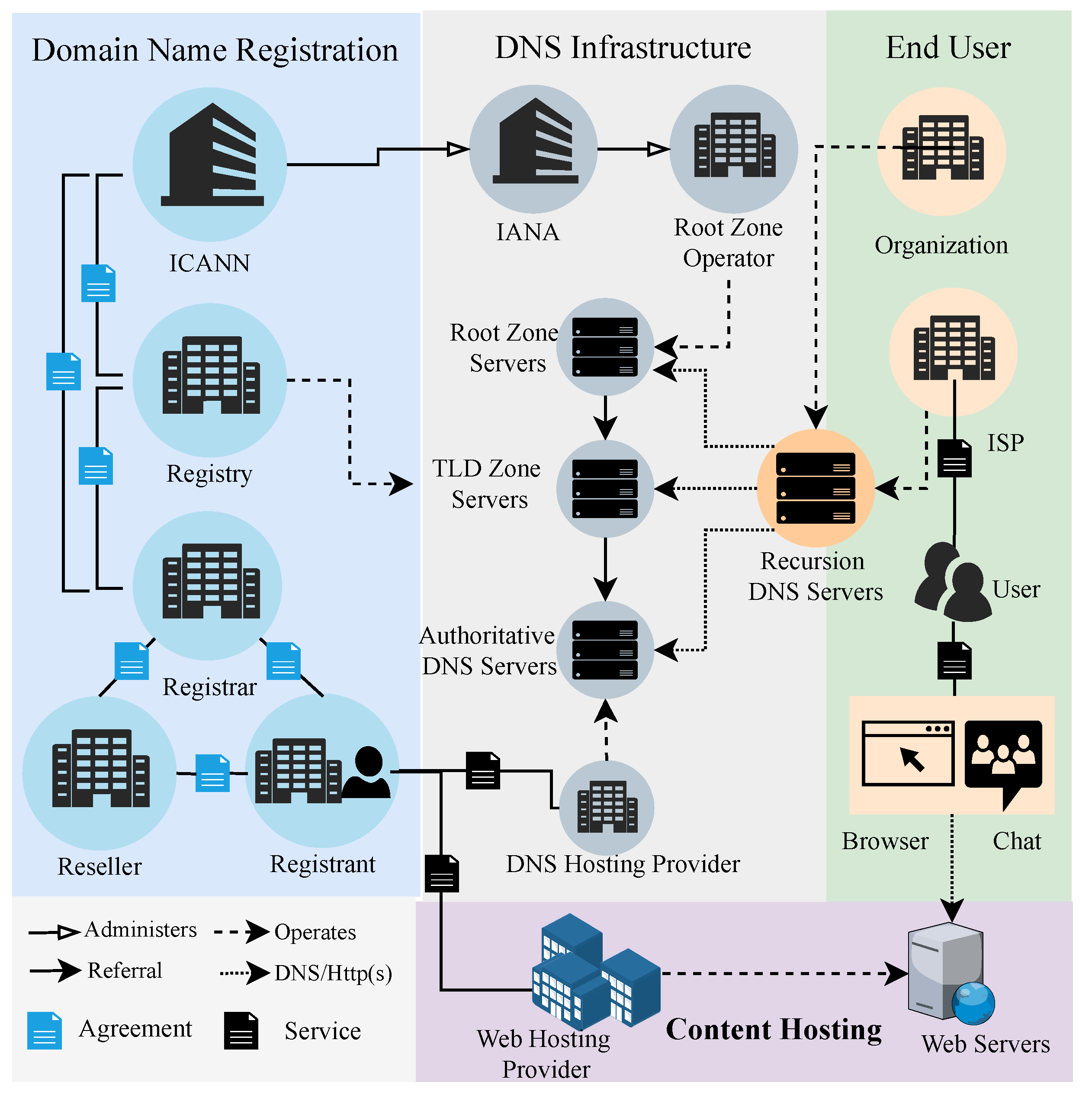
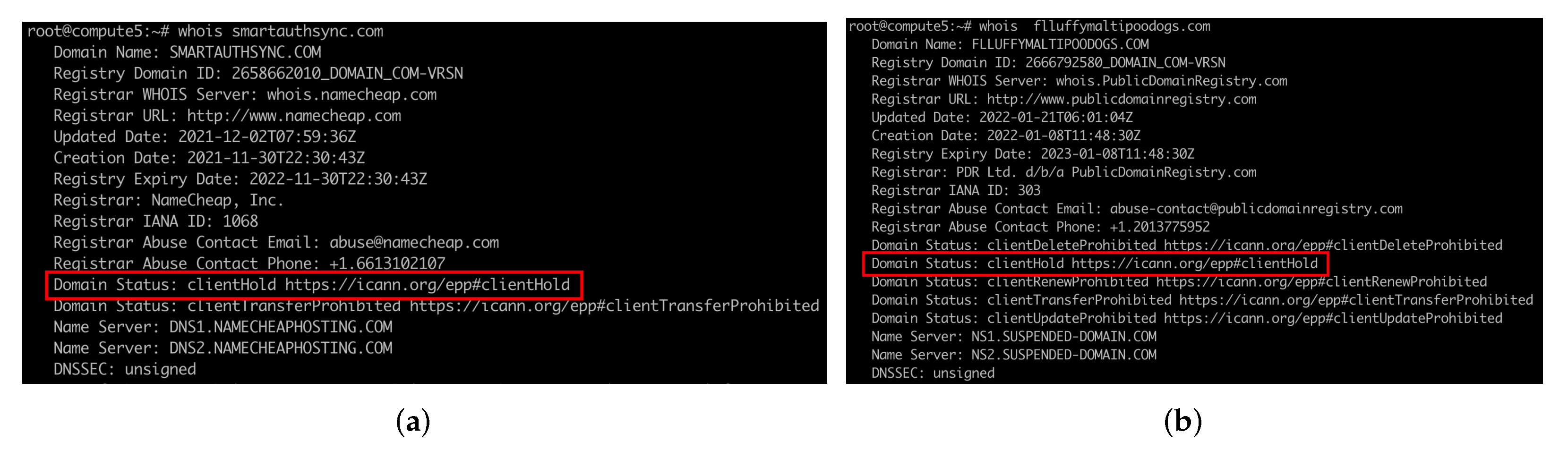
Electronics | Free Full-Text | Evaluating the Effectiveness of Handling Abusive Domain Names by Internet Entities
Compromised Sites and Malicious Registrations: Best Practices for the Identification and Mitigation of DNS Abuse - DNS Abuse Institute

Abuse Management for Domain Names - Cybersecurity & Data Protection – Public Security & Individual Freedom: doteditorial - Security & Trust in Digital Services - Issues - dotmagazine