Organizations worldwide call for a stronger response to technology-based trafficking — Freedom Collaborative

Australian Federal Police - The Australian Centre to Counter Child Exploitation has led an Australia wide police operation, as part of a larger international effort, targeting a website selling abhorrent child abuse
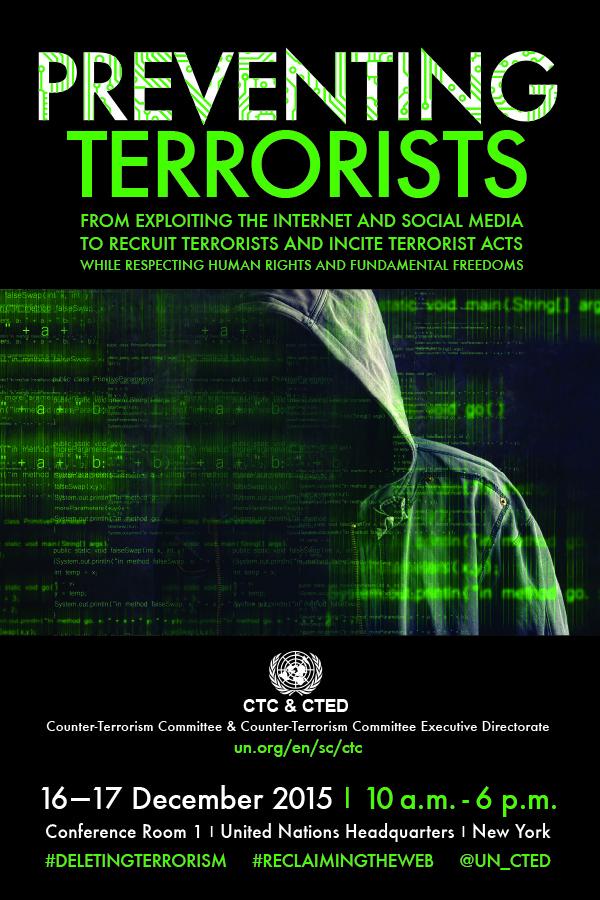
Special meeting of the Counter-Terrorism Committee and technical sessions of the Counter-Terrorism Committee Executive Directorate on preventing and combating abuse of ICT for terrorist purposes, New York, 16-17 December 2015 | Security

TikTok joins Technology Coalition to counter online sexual exploitation and abuse - Campaign Middle East

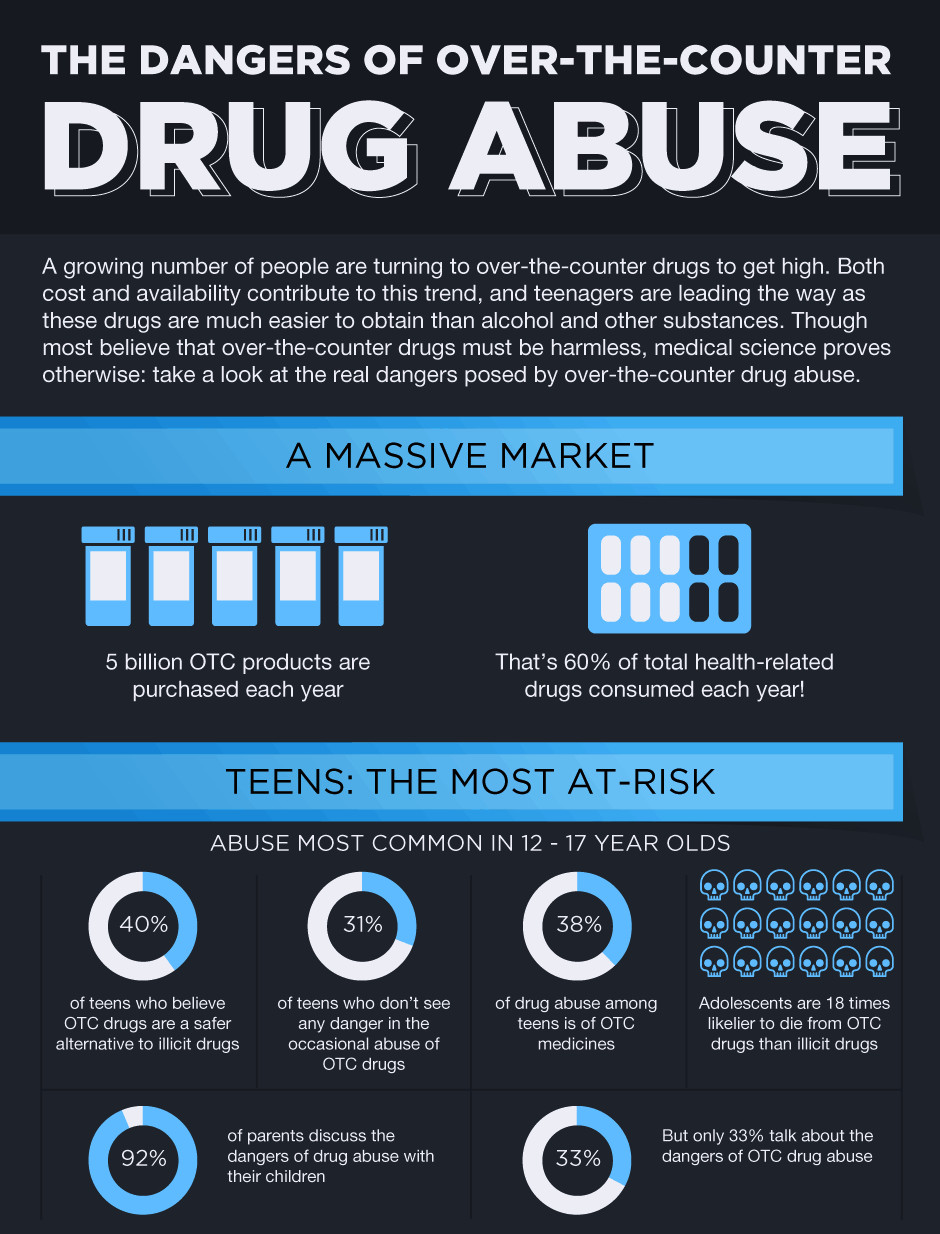
State Level Convening on "Use and Abuse of Technology in Human Trafficking". | technology | State Level Convening on "Use and Abuse of Technology in Human Trafficking". #राज्य_महिला_आयोग #मुंबई | By Rupali Chakankar | Facebook